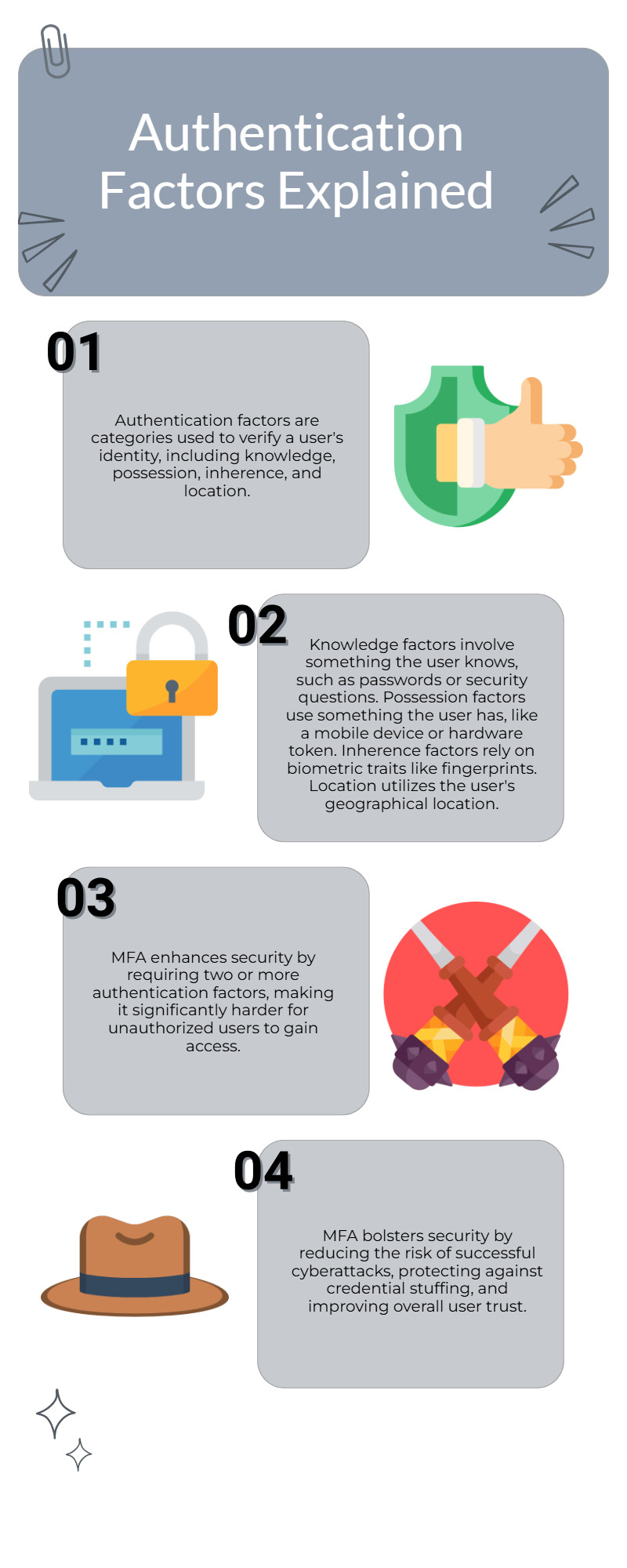
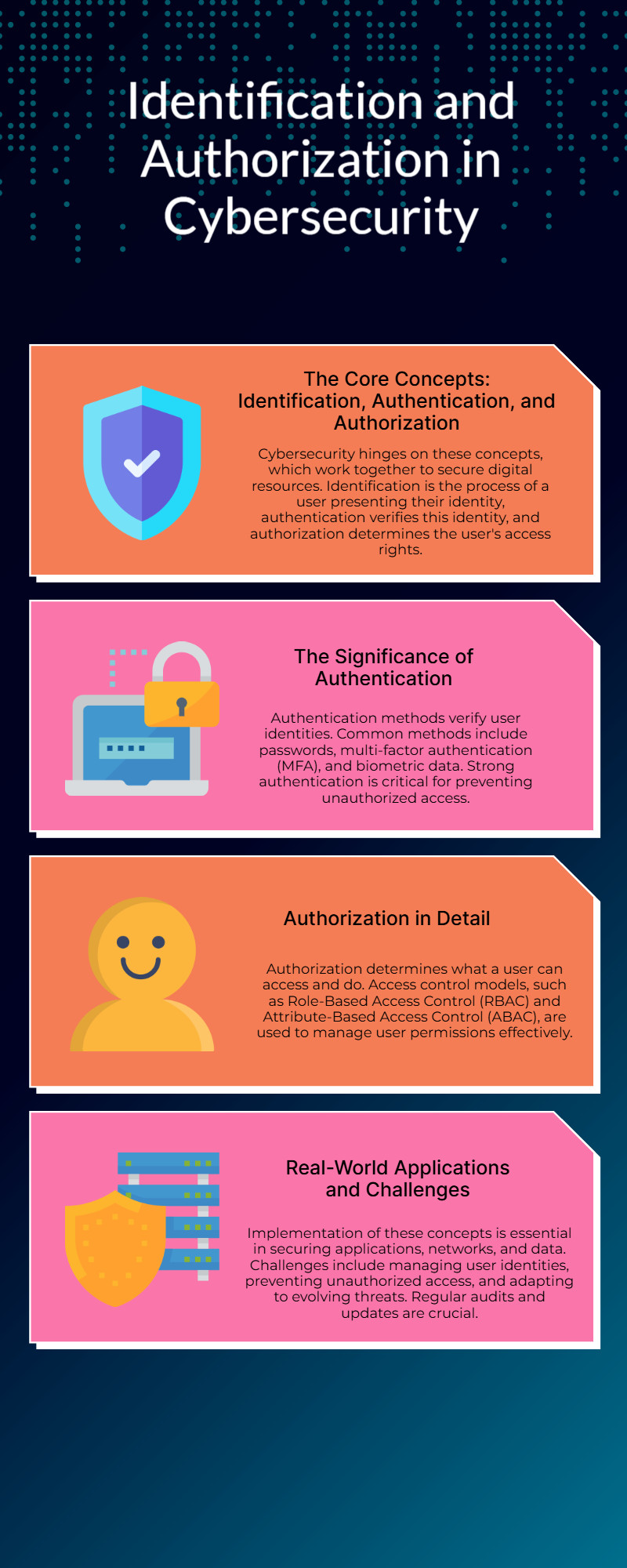
Understanding the Security Levels of 1FA, 2FA, and MFA
Understanding the differences between 1FA vs 2FA vs MFA is key to strengthening your digital security. This blog breaks down the security levels of each method - explaining how single-factor authentication (1FA) relies on just one credential, two-factor authentication (2FA) adds an extra layer, and multi-factor authentication (MFA) provides the most robust protection.
More Info - https://www.loginradius.com/bl....og/identity/authenti